Coupang (CPNG): Q4 2025 Earnings Review
I wrote back in January that I thought the Coupang selloff was overdone and that I was buying. The stock went on to fall another 10% after that post, bottoming out around $17 and change. It's since bounced back to around $19, but we're still down over ~40% from the September highs.

Q4 results came out about a week and half ago, and I actually feel a lot better about the position now than I did when I first wrote it up. For the first time we have actual forensic data from Mandiant and Palo Alto Networks on what happened with the breach.
Management walked through the findings in detail on the call. And the picture that’s emerging is very different from the one the market priced in.
The core business was growing ~16% in constant currency right up until December. The breach knocked the wind out of it for one month, January looks like it was the trough, and things are already recovering. Meanwhile the stock is still trading near its lowest multiples ever and the market seems to have completely forgotten that Taiwan exists.
There’s a lot to get into here, so let me just walk through it and share where my head’s at.
Q4 Highlights
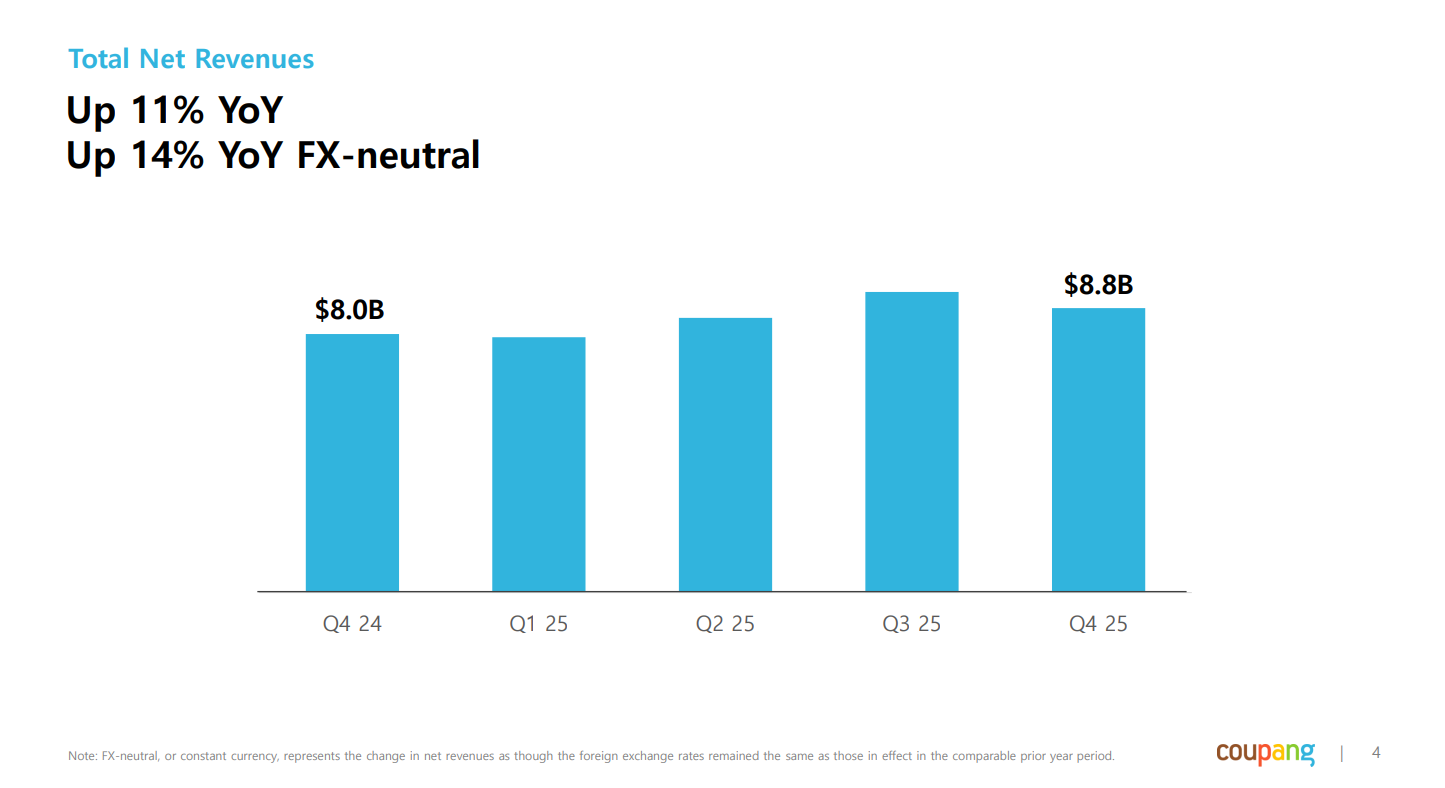
Total revenue was $8.8 billion, up 11% year-over-year or 14% in constant currency. That’s a step down from the 18% constant currency growth they posted in Q3, and basically all of the deceleration traces back to December when the breach started hitting customer behavior.
Product Commerce did $7.4 billion, up 12% constant currency. But for the three months before December, the business was running at a completely different pace. From the CFO on the call:
“For the three-month period prior to December, Product Commerce was bringing strong revenue growth of 16% in constant currency. And we believe the softening of those growth rates reached the lowest levels in Jan with an estimated 4% constant currency growth rate adjusted to the timing of Lunar New Year holiday. And we have seen improving trends since then.”
So the organic business was humming along just fine, the breach news hit, people panicked, some deleted accounts, and the month fell off. January was the trough and February is already improving…
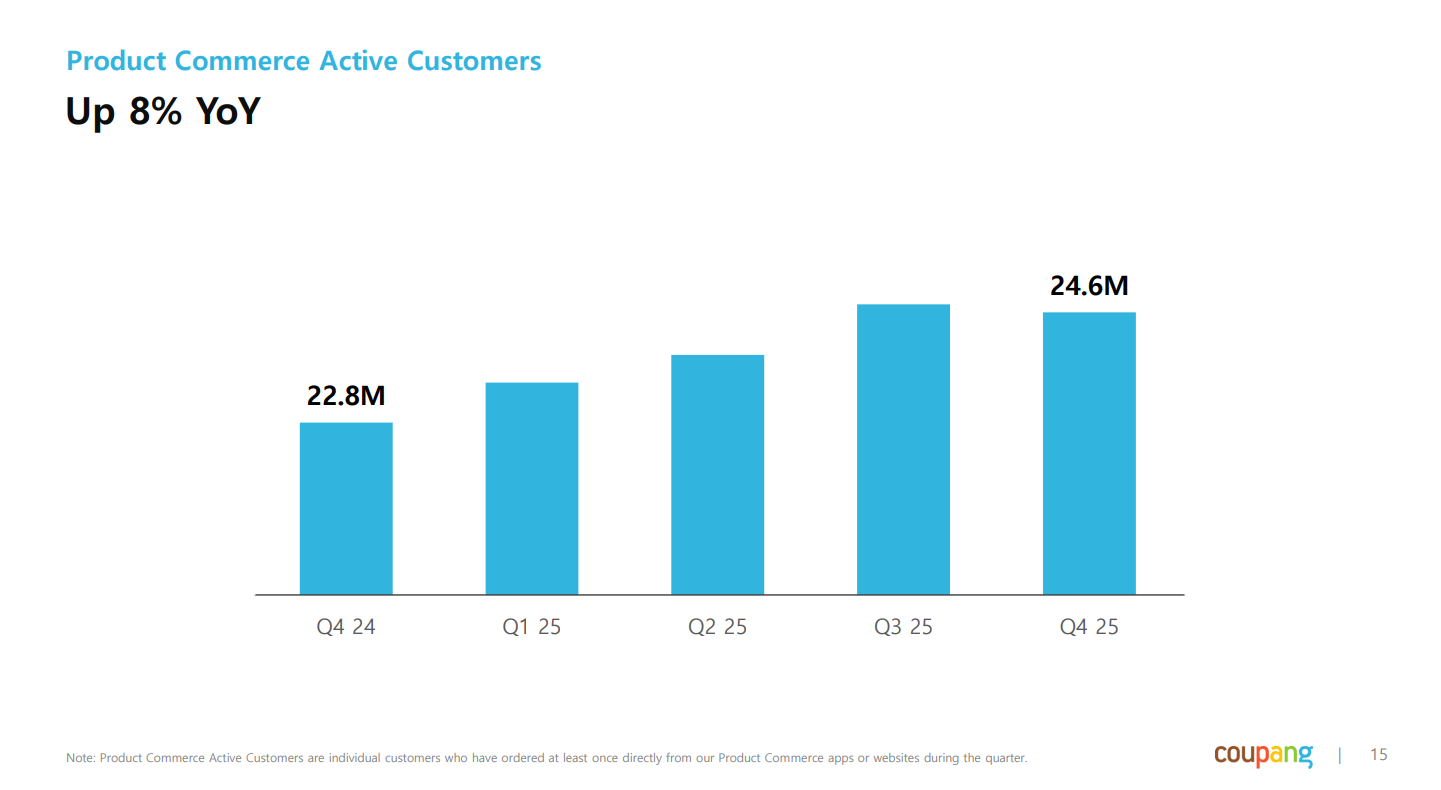
Active customers came in at 24.6 million, up 8% year-over-year but slightly down from Q3’s 24.7 million, and WOW membership saw elevated churn in December. Again, all of it concentrated in that one month.
Product Commerce EBITDA was $567 million at a 7.7% margin. If you strip out a one-time fire insurance gain from the prior year comp, margins actually improved 85 basis points year-over-year. The core business is still getting more efficient and that part is getting completely overlooked.
Consolidated EBITDA was $267 million, down 37%. That looks terrible until you realize it’s the combination of December softness and the fact that Developing Offerings (Taiwan, Eats, Farfetch) lost $300 million in the quarter. The core Korean business is doing just fine.
Free cash flow for the year was $527 million, down from about $1 billion last year, mostly because working capital got hit in Q4 from the breach and capex is ramping as they build out Taiwan.
Overall it was a decent quarter all things considered and nothing really stood out as a reason for concern.
Ok, the Breach. Let’s Talk About It.
This is what everyone cares about at the moment so I’m going to spend some time here.
My view hasn’t really changed since my January post, but the Q4 call gave us something we didn’t have before: actual forensic results from Mandiant and Palo Alto Networks. And the findings are about as good as you could hope for given the circumstances.
Harold Rogers, the General Counsel, walked through the whole thing on the call.
A former employee, a 43-year-old Chinese national who left the company in 2024, kept his access credentials and used them to poke around the database over about five months. Coupang detected unusual activity in early November. The guy technically accessed 33 million accounts but only retained data from roughly 3,000 of them, and he later deleted it.
They recovered his laptop from a river. He’d thrown it in weighted down with bricks, packed inside a Coupang delivery bag. I’m sorry but that detail is still wild to me… lol
Here’s what Rogers said on the call:
“Third-party forensics and cybersecurity experts, including Mandiant, have confirmed that no highly sensitive data was ever accessed. No financial data, no passwords, and no government issued IDs were compromised.
All of the former employees’ devices known to have been used in the attack have been recovered. Mandiant has also found that the forensic evidence is consistent with the conclusion that the former employee retained data from approximately 3,000 user accounts in Korea and one user account in Taiwan and later deleted the data. Importantly, there is no evidence that any of that data was ever viewed by anyone else. This is also supported by the fact that there have been zero confirmed instances of any of this customer data being exploited.
We have retained the services of multiple outside experts to monitor, among other places, the dark web and deep web, including CNSecurity. To date, there has been no detection of the misuse of customer data attributable to the incident, nor is there evidence that any Coupang user data attributable to the incident exists in those sources. The Korean National Police Agency and the government’s investigative organization, the JIT, have also indicated that they have found no evidence of any misuse of customer data or any secondary harm resulting from this incident to-date.
Palo Alto Networks, one of the world’s foremost cybersecurity firms, concluded from their investigation that “Coupang’s security controls are aligned with industry standards. The recent incident was not caused by a systemic failure of security measures but was the result of a targeted attack executed by a malicious, former employee who leveraged inside knowledge of systems and exploited a valid software development process.” This was a crime committed by a former employee against Coupang and against our customers. We have called for him to be brought to justice and prosecuted to the fullest extent of the law.” — Harold Rogers
The narrative that’s been floating around is that Coupang had some kind of negligent security failure and millions of customers had their financial data stolen. The forensics clearly say otherwise.
The company’s cybersecurity spend has been top three among all companies in Korea for the past four years. A former employee abused a position of trust and committed a crime. It happens, and Coupang clearly needs to tighten up their offboarding procedures, but this is not the story the headlines told.